Why Agent Authority Must Be Centralized
Every team is building agents. Few are designing the authority those agents exercise.
The Problem with Decentralized Authority
Authority is a decision right. Not a role. Not a permission. A decision right — the explicit, scoped, enforceable right to act within defined boundaries.
Agent governance today follows a familiar pattern. Each team embeds its own authority model — as prompt engineering, system instructions, or hardcoded logic — inside whatever agent it happens to be building. The authority is invisible to everyone else. It lives in code, not in a format anyone outside the team can read, review, or audit.
This is not a coordination failure. It is a constitutional one.
When authority is embedded inside agents, three things happen simultaneously. Visibility disappears — business teams cannot see what decision rights the agent actually exercises because the authority model is hidden in prompts or code. Portability vanishes — authority is tied to one agent or platform, and switching means reconstructing the entire decision framework from scratch. Governance becomes impossible — there is no separation between who grants authority and who exercises it.
The result is not chaos. It is something worse: the appearance of governance without the substance. Each team believes its agents are governed. The organization has no way to verify that claim. Authority was exercised. It was never designed.
What Happens When Every Team Defines Its Own Authority
Three teams in the same organization build agents that touch budget approval flows. Procurement builds an agent that routes purchase requests and validates vendor terms. Regional operations builds an agent that pre-approves travel and event budgets. Finance builds an agent that reviews quarterly spend against forecasts and flags overruns.
Each team defines its own authority boundaries — approval thresholds, escalation rules, documentation requirements. Each set of boundaries is reasonable in isolation. None of them are consistent with each other.
The procurement agent auto-approves purchases under $10,000 with no secondary review. The regional operations agent requires VP sign-off for anything over $2,500. The finance agent flags spend deviations above 15% — but the procurement agent has no deviation threshold at all. Regional operations logs every approval decision to a shared audit trail. Procurement logs nothing.
No single team made a bad decision. The organization made no decision at all. Authority was never granted — it was assumed, per team, per agent, per sprint.
That gap — between authority exercised and authority designed — is where instability originates. Not because teams lack constraints, but because decision rights are local when the consequences are organizational.
One Process, One Authority Model, Every Client
Centralized authority does not mean centralized control. It means a single source of truth for what decision rights exist, who holds them, and under what conditions they apply — regardless of which agent exercises them, which platform hosts them, or which team initiates them.
With SOP-MCP, the authority model lives outside the agent. It is written in plain markdown with RFC 2119 requirement levels that define the structure of decision rights for each process. As we explored in the previous post, MUST/SHOULD/MAY creates a graduated authority framework — boundaries, defaults, and delegated discretion. The structural point here is different: that framework only works if it is singular.
Two teams cannot independently define the approval threshold for the same spend category. Two agents cannot exercise contradictory authority over the same data. The moment the authority model is duplicated — embedded separately in each agent — it ceases to be an authority model. It becomes a collection of local assumptions.
A single SOP, served through a single protocol, consumed by any MCP-compatible client. The authority structure is defined once. Every agent that exercises it gets the same boundaries, the same discretion, the same delegation — regardless of platform.
When the CFO changes the approval threshold from $10,000 to $5,000, that change propagates to every agent across every platform through one SOP update. No redeployment. No coordination across teams. No hoping that each team remembers to update its own embedded rules.
What Centralized SOP-MCP Looks Like
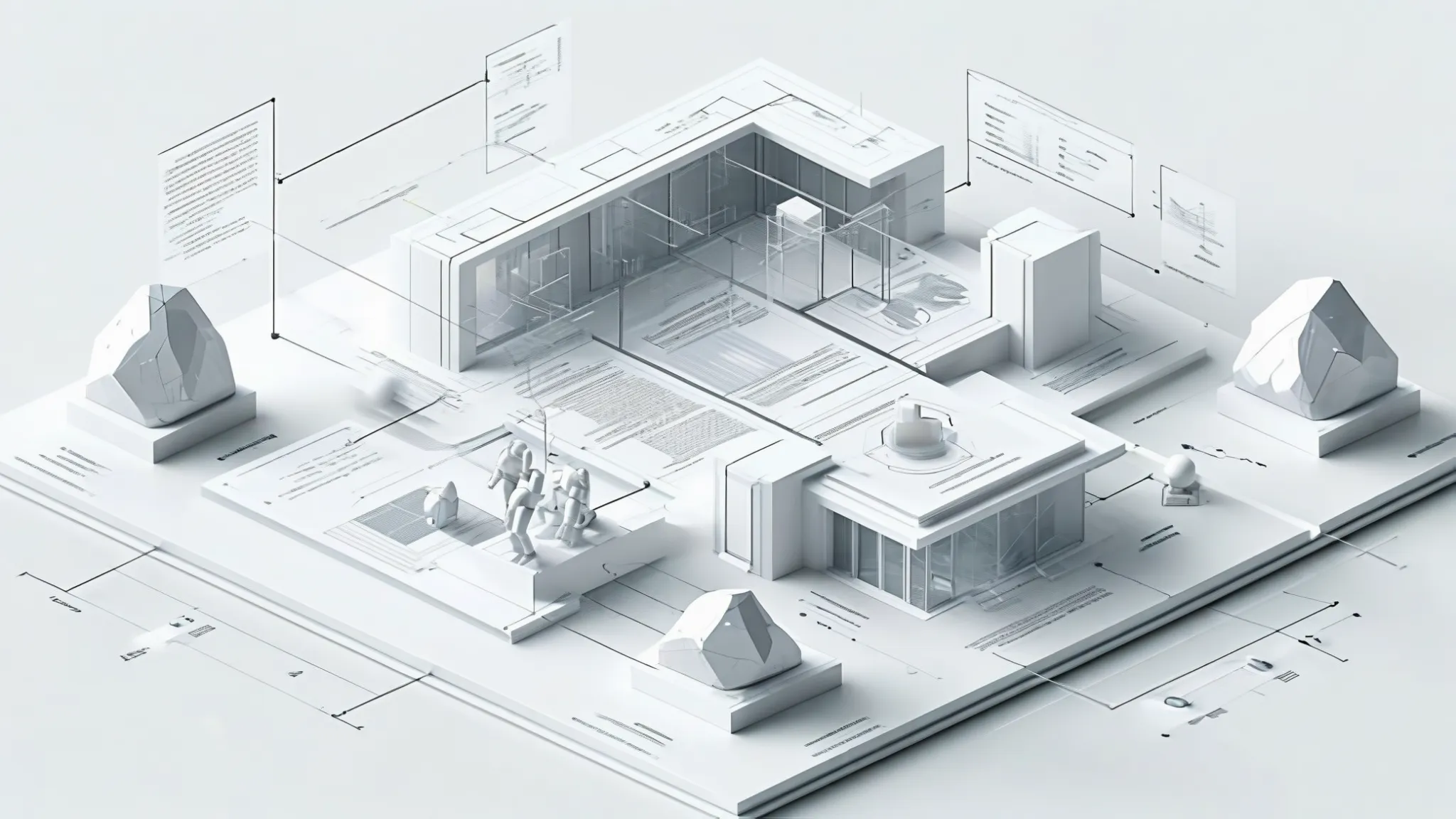
The architecture separates four concerns that most implementations conflate.
Process intent is the SOP itself — what decision rights exist, in what sequence, with what requirements. Execution runtime is the agent that exercises those rights — which LLM, which tools, which integrations. Governance control is the mechanism that enforces authority — who can grant, modify, and revoke decision rights, and under what audit and compliance constraints. Client platform is where the human interacts — or where no human interacts at all, for fully autonomous execution.
Each layer changes independently. Process owners update authority models without touching runtime or governance. Platform teams swap agents or LLMs without redefining decision rights. Security teams update policies without modifying business logic.
This is not a theoretical separation. It is the difference between defining authority in one place and reconstructing it inside every agent that happens to exercise a copy.
Who Grants Authority?
Centralized authority raises an immediate question: who decides what decision rights agents hold?
The answer is not the engineering team. The person who knows when a purchase order requires secondary review is the procurement director. The person who knows which spend categories require CFO approval is the finance controller. The person who knows the documentation requirements for audit compliance is the risk manager.
Authority must be defined by the people who own the domain, in language they already use. SOP-MCP makes this possible because the format is markdown — not code, not configuration, not a proprietary DSL. Domain experts define the authority structure. Engineers wire the integrations. The separation is clean.
Access control reinforces this separation through three permission tiers. Execute permissions control who can exercise authority — per process, per department, per role. Publish permissions control who can grant or modify authority — process owners only, preventing agents from rewriting their own decision rights without human oversight. Feedback permissions are intentionally open — anyone who executes a process can submit improvement suggestions.
Different teams own different authority domains within the same system. Procurement owns purchase approval. Finance owns spend review. HR owns headcount authorization. The catalog is unified. Access is filtered by policy. One system, many authority owners, separation through authorization — not duplication.
From Local Tool to Organizational Infrastructure
The trajectory is predictable. Teams start with one SOP for one process. It works. They write another. Other teams notice. The question shifts from “should we use this?” to “how do we govern this at scale?”
This is where centralized authority stops being a convenience and becomes a structural requirement. When SOPs are versioned and observable, they generate execution data — which decision rights were exercised, how long each step took, where handoffs happened, where the process stalled.
That data is only useful if it is centralized. If each team runs its own SOP server with its own telemetry, the organization cannot reason across authority boundaries. It cannot detect that the procurement approval SOP stalls because it depends on output from the vendor validation SOP that is always late. It cannot identify that two teams exercise contradictory authority over the same spend category because neither team can see the other’s authority model.
Organizational intelligence requires organizational visibility. Organizational visibility requires centralized authority. The dependency is structural, not political.
The Structural Claim
Decentralized agent authority is not governance. It is the absence of authority distributed across teams, each believing the problem is solved locally.
Centralized authority through SOP-MCP does not remove team autonomy. It makes decision rights explicit, scoped, and enforceable — a single place where authority is defined, versioned, observed, and improved. The agent is the execution engine. The SOP is the authority model. The gateway is the enforcement boundary. Governance follows from that structure. It does not precede it.
Authority that is not designed is authority that is not governed. And authority that is not governed is authority that will be exercised without legitimacy — until the consequences make the structural gap visible.